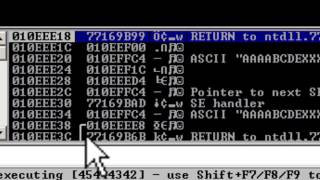
Web Reference: When a user supplied input is sent to a program vulnerable with a buffer overflow vulnerability, the stack is overwritten from lower memory addresses towards higher memory addresses. After passing the exception EIP and ESP are overwritten, with values from my buffer, yet other registers are zeroed out (EAX, EBX, ESI & EDI in my example). So I can control EIP and ESP, but the tutorials mention that it is useless, due to the zeroed out registers.However, they never explain why the zeroed out registers are the problem - so here is... Jul 25, 2009 · In the first 2 parts of the exploit writing tutorial series, I have discussed how a classic stack buffer overflow works and how you can build a reliable exploit by using various techniques to jump to the shellcode.
YouTube Excerpt: A college course in
Net Worth Profile Overview
Seh Stack Buffer Overflow Net Worth 2026: Salary, Income & Wealth Net Worth & Biography

Estimated Worth: $35M - $74M
Salary & Income Sources

Career Highlights & Achievements
Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 9, 2026
Net Worth Outlook & Future Earnings

Disclaimer: Disclaimer: Net Worth estimates are based on publicly available data, media reports, and financial analysis. Actual numbers may vary.